Vulnerability Details
CVE ID: CVE-2017-12939
Type: Remote Code Execution
Discovered: 2017/08/13
Discovered By: Rio
Patch Availability: 2017/08/18
Affected Operating System: Windows
Affected Versions: All (Windows)
Severity: High
Patch Versions:
- [1] 5.3.8p2 (Win) (Mac)
- [2] 5.4.5p5 (Win) (Mac)
- [3] 5.5.4p3 (Win) (Mac)
- [4] 5.6.3p1 (Win) (Mac)
- [5] 2017.1.0p4 (Win) (Mac)
- [6] 2017.2.0b8 (Win) (Mac)
Please note: The Mac version is provided as a courtesy for team environments using Windows and Mac. The Mac version is NOT affected by the identified vulnerability.
If a patch is not available for your version, please use the Mitigation Tool [7] (All versions).
An input string validation issue was identified in the Unity Editor affecting the Windows platform that could lead to Remote Code Execution (RCE), allowing an attacker to potentially execute code remotely in the user’s computer.
Remediation Steps
Determine the version of your Unity Editor
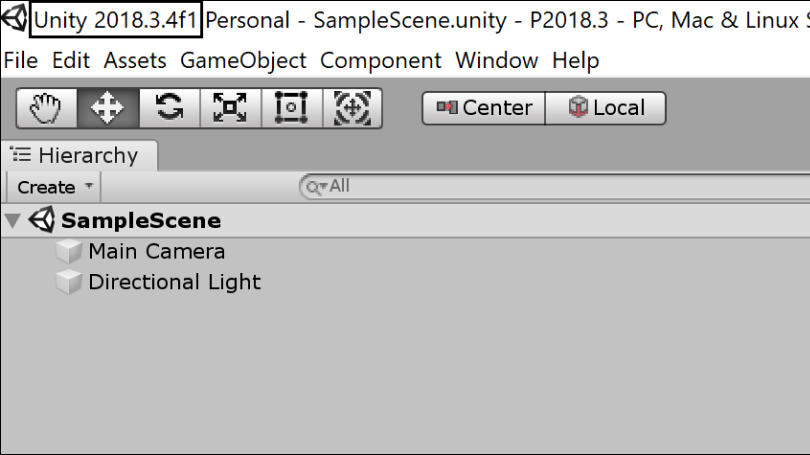
Open a Unity project.
The Unity version is visible in the main window title.
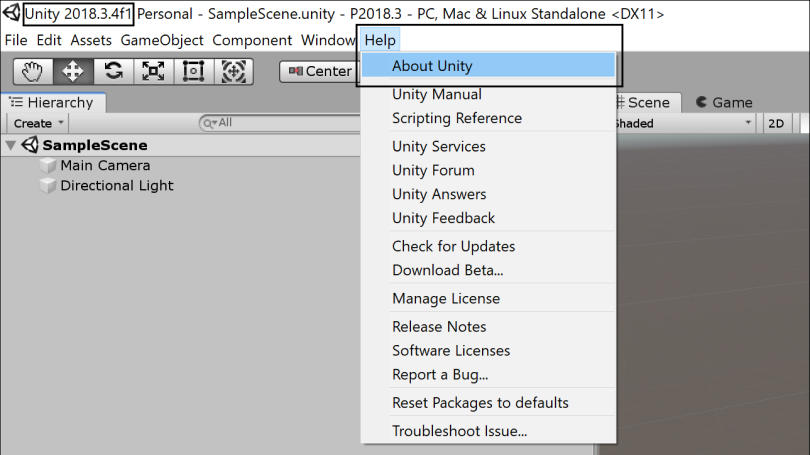
In the File menu choose Help -> About Unity.
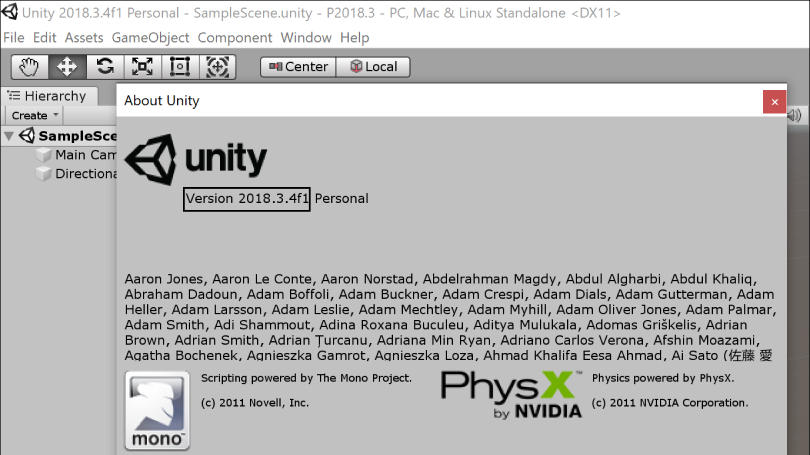
The Unity version is shown in the About Unity window.
Install Update
If your version of the Unity Editor is not one of the listed in the Patch Versions of the Vulnerabilities Details section above you can continue with the update installation as follows.
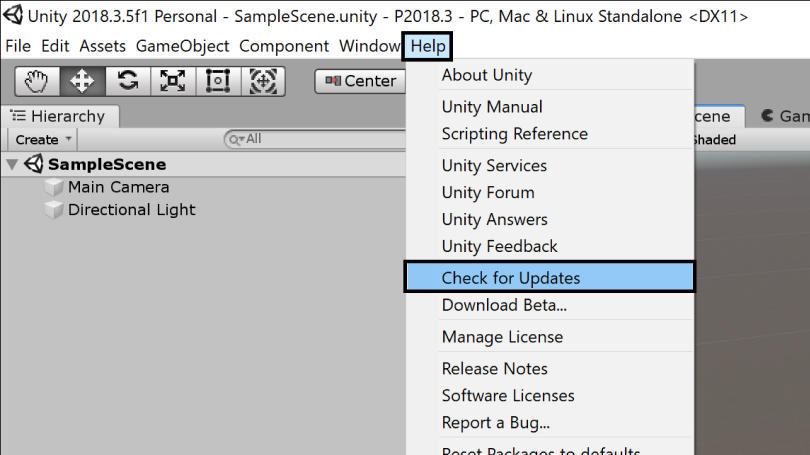
To install the update you can use the Unity Editor update checker available in the File menu Help -> Check for Updates.
Additionally, you can download and install the corresponding patch for your version of the Unity Editor. The download links are available in the Patch Versions of the Vulnerabilities Details section and in the References section.
Mitigation Tool
If your version of the Unity Editor is not listed, or you are unable to install the update at this time, you can use the Mitigation Tool Guide [7].
Please keep in mind the recommended action is to install a fixed version of the Unity Editor.
FAQ
An input string validation issue was identified that could lead to remote code execution (RCE), allowing an attacker to potentially execute code remotely in the user’s computer.
No. Only the Unity Editor is affected.
Windows only. Mac and Linux platforms are not affected by the identified vulnerability.
All versions of Windows.
All versions of the Unity Editor running on Windows.
We have released a patch for the following Unity versions: 5.3, 5.4, 5.5, 5.6, and 2017.1. The full details are listed on this page.
We will not be patching Unity 4.x, 5.0, 5.1, or 5.2.
Unity will be releasing a single patch to each of the most current dot-releases of Unity. For example, users running an older version of Unity 5.3 will need to update to the patched version of 5.3.8. There will be no patches for 5.3.7, 5.3.6, etc.
We are providing a workaround tool that disables the identified vulnerable Unity Editor feature, which can be downloaded from Mitigation Tool Guide [7]. Please understand, though, that the workaround is not a patch and has limitations. The workaround will disable the Unity Editor feature identified as vulnerable, but since we can’t control whether the affected functionality becomes re-enabled at some point after applying the workaround (system changes, reinstallations, etc.), we strongly recommend updating to the latest version of Unity to get the benefits of the full patch. You will also no longer be able to use the ‘Open in Unity’ functionality in the web browser version of the Asset Store after applying the workaround.
The updates are available here, in the Patch Versions section.
The workaround tool can be used on all affected versions of Unity. Please understand, though, that the workaround is not a patch and has limitations: the workaround will disable the identified vulnerable Editor features, but since we can’t control whether the affected functionality becomes re-enabled at some point after applying the workaround (system changes, reinstallations, etc.), we strongly recommend updating to a patched version. You will also no longer be able to use the ‘Open in Unity’ functionality in the web browser version of the Asset Store after applying the workaround.
No, by running it once it deactivates the identified vulnerable component across all of them. Do keep in mind that by re-installing or updating (one) of the versions, it may activate the component again. To check, re-run the workaround tool until all versions are up to date.
The workaround will disable the Unity Editor feature identified as vulnerable, but since we can’t control whether the affected functionality becomes re-enabled at some point after applying the workaround (system changes, reinstallations, etc.), we strongly recommend updating to a patched version. You will also no longer be able to use the ‘Open in Unity’ functionality in the web browser version of the Asset Store after applying the workaround.
The updates are available here, in the Patch Versions section.
Our focus right now is on addressing the identified vulnerability in the most current version of each dot-release. We don’t have any details to share on patches for other versions at this time.
It depends on the specific version of Unity that you are using. Most customers will be able to update to the patched versions without needing to rebuild their bundles, but some customers may find that asset importers have been updated between the version they’re currently using and the patch for that dot-release. For those customers, asset bundle rebuilding may be necessary.
You definitely won’t need to rebuild bundles if you’re currently using 5.3.8p1, 5.4.5p4, 5.5.4p2, 5.6.3f1, or 2017.1.0p3.
You may need to rebuild your bundles if any assets are re-imported when you first open your project in the patched version of Unity.